下载 macOS Sonoma 14.8.4 的安装包
查看签名信息
/Users/wnagzihxa1n/Security/macOS/固件提取 > pkgutil --check-signature InstallAssistant.pkg
Package "InstallAssistant.pkg":
Status: signed Apple Software
Certificate Chain:
1. Software Update
Expires: 2029-04-14 21:28:23 +0000
SHA256 Fingerprint:
E0 74 D2 04 AC 24 98 E9 DC 90 4A 7B C7 CE D8 46 41 19 B7 9D 05 66
80 28 92 05 83 B1 E8 96 EB B4
------------------------------------------------------------------------
2. Apple Software Update Certification Authority
Expires: 2031-10-15 00:00:00 +0000
SHA256 Fingerprint:
12 99 E9 BF E7 76 A2 9F F4 52 F8 C4 F5 E5 5F 3B 4D FD 29 34 34 9D
D1 85 0B 82 74 F3 5C 71 74 5C
------------------------------------------------------------------------
3. Apple Root CA
Expires: 2035-02-09 21:40:36 +0000
SHA256 Fingerprint:
B0 B1 73 0E CB C7 FF 45 05 14 2C 49 F1 29 5E 6E DA 6B CA ED 7E 2C
68 C5 BE 91 B5 A1 10 01 F0 24
解压缩
➜ /Users/wnagzihxa1n/Security/macOS/固件提取 > pkgutil --expand-full InstallAssistant.pkg expanded
/Users/wnagzihxa1n/Security/macOS/固件提取 > cd expanded
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded > ls -al
drwxr-xr-x@ 9 wnagzihxa1n staff 288 Apr 12 16:53 .
drwxr-xr-x 5 wnagzihxa1n staff 160 Apr 12 16:48 ..
-rw-r--r--@ 1 wnagzihxa1n staff 275808 Feb 1 04:40 Bom
-rw-r--r--@ 1 wnagzihxa1n staff 918 Apr 12 16:48 PackageInfo
drwxr-xr-x@ 4 wnagzihxa1n staff 128 Apr 12 16:48 Payload
drwxr-xr-x@ 4 wnagzihxa1n admin 128 Apr 12 16:48 Scripts
-rw-r--r--@ 1 wnagzihxa1n staff 13646176379 Feb 1 04:40 SharedSupport.dmg
提取SharedSupport.dmg中的com_apple_MobileAsset_MacSoftwareUpdate
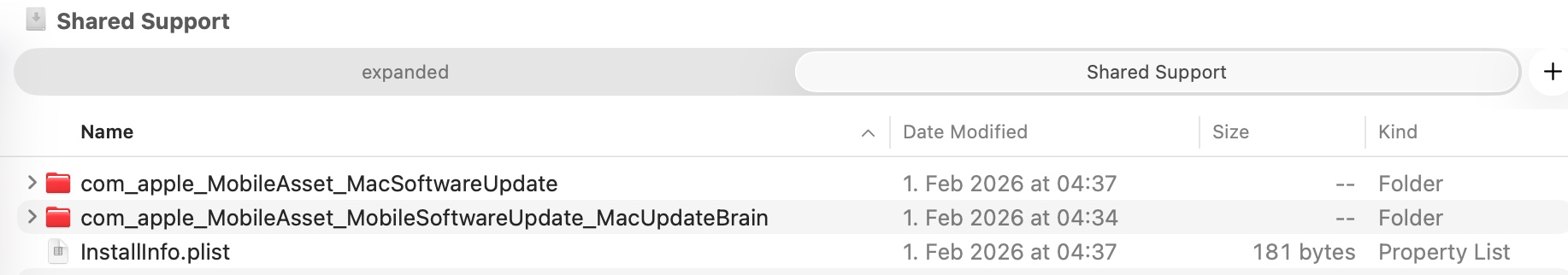
这个目录下还有一个很大的压缩包
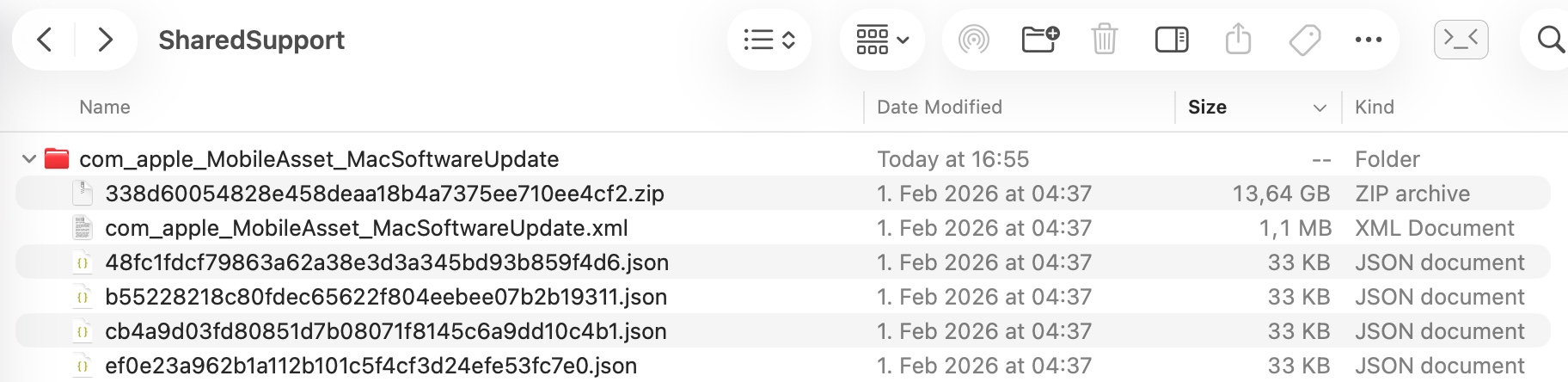
再提取com_apple_MobileAsset_MacSoftwareUpdate下的338d60054828e458deaa18b4a7375ee710ee4cf2.zip
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2 > ls -al
total 32
drwx------ 6 wnagzihxa1n staff 192 Apr 12 19:57 .
drwxr-xr-x 81 wnagzihxa1n staff 2592 Apr 12 16:55 ..
drwxr-xr-x 17 wnagzihxa1n staff 544 Apr 12 20:25 AssetData
-rw-r--r-- 1 wnagzihxa1n staff 5456 Feb 1 04:10 Info.plist
drwxr-xr-x 3 wnagzihxa1n staff 96 Feb 1 04:10 META-INF
进入目录AssetData,目录中就是要进行处理的二进制数据
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2/AssetData > ls -al
total 90648
drwxr-xr-x 17 wnagzihxa1n staff 544 Apr 12 20:25 .
drwx------ 6 wnagzihxa1n staff 192 Apr 12 19:57 ..
drwxr-xr-x 21 wnagzihxa1n staff 672 Feb 1 03:40 boot
-rw-r--r-- 1 wnagzihxa1n staff 2210 Feb 1 04:08 Info.plist
drwxr-xr-x 4 wnagzihxa1n staff 128 Apr 12 16:57 payload
-rw-r--r-- 1 wnagzihxa1n staff 447426 Feb 1 04:10 payload.bom
-rw-r--r-- 1 wnagzihxa1n staff 128 Feb 1 04:10 payload.bom.signature
drwxr-xr-x 97 wnagzihxa1n staff 3104 Apr 12 16:58 payloadv2
-rw-r--r-- 1 wnagzihxa1n staff 483474 Feb 1 04:09 payloadv2.bom
-rw-r--r-- 1 wnagzihxa1n staff 128 Feb 1 04:09 payloadv2.bom.signature
-rw-r--r-- 1 wnagzihxa1n staff 45411154 Feb 1 03:41 post.bom
-rw-r--r-- 1 wnagzihxa1n staff 35046 Feb 1 03:41 pre.bom
drwxr-xr-x 8 wnagzihxa1n staff 256 Apr 12 16:57 Restore
drwxr-xr-x 4 wnagzihxa1n staff 128 Apr 12 16:57 usr
先创建extracted文件夹用于存储解析后的文件,同时使用如下脚本,对二进制数据进行解析
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2/AssetData > mkdir extracted
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2/AssetData > for i in $(seq -f "%03g" 0 42); do
python3 ./extracted/pbzx.py < payloadv2/payload.$i
done > ./extracted/payload.aa
pbzx.py文件的内容如下
import sys, struct, lzma
def pbzx_stream(input_stream, output_stream):
magic = input_stream.read(4)
assert magic == b'pbzx', f"Not a pbzx stream, got: {magic}"
input_stream.read(8) # skip global flags
while True:
header = input_stream.read(16)
if len(header) < 16:
break
chunk_flags = struct.unpack('>Q', header[0:8])[0]
chunk_size = struct.unpack('>Q', header[8:16])[0]
chunk_data = input_stream.read(chunk_size)
if len(chunk_data) < chunk_size:
break
# 用 XZ 魔数检测,而不是依赖 flag 位
if chunk_data[:6] == b'\xfd7zXZ\x00':
output_stream.write(lzma.decompress(chunk_data))
else:
output_stream.write(chunk_data)
pbzx_stream(sys.stdin.buffer, sys.stdout.buffer)
完成后在extracted目录下就会生成payload.aa文件
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2/AssetData > ls -lh extracted/payload.aa
-rw-r--r--@ 1 wnagzihxa1n wheel 14G Apr 12 20:14 extracted/payload.aa
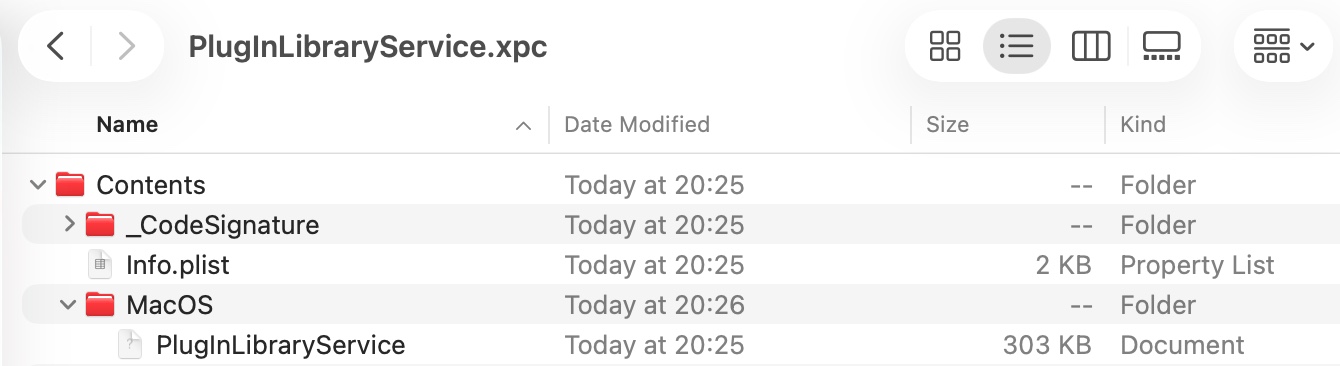
现在开始提取PlugInLibraryService.xpc文件
/Users/wnagzihxa1n/Security/macOS/固件提取/expanded/SharedSupport/com_apple_MobileAsset_MacSoftwareUpdate/338d60054828e458deaa18b4a7375ee710ee4cf2/AssetData > aa extract -i ./extracted/payload.aa -d ./extracted/ -include-path "System/Library/Frameworks/NetFS.framework/Versions/A/XPCServices"
右键PlugInLibraryService.xpc文件,点击显示文件内容,接下来就可以开始进行后续的逆向分析了